Everyone Talks About the Cloud These Days
Everyone talks about the Cloud these days, but many people’s understanding of it remains, well, cloudy. What is it? Why is it called the Cloud? How do you use it? Is it secure?
There are lots of long answers to these questions, but in a nutshell, the Cloud is the internet. It’s where you store and access data instead of using your computer’s hard drive or company’s data storage system (that’s referred to as “on prem,” for “on premises”). This means you access programs and storage capacity from the internet via your web browser, and the expense and logistics of maintaining equipment and developing and updating software programs are managed by another entity—the Cloud provider (CP).
It’s called the Cloud because the CP’s hardware and software locations have no bearing on your ability to use those services—they are “just out there, somewhere,” like a cloud floating by in the sky. Of course, someone does own and maintain this actual hardware and software. The three largest public CPs—Amazon Web Services (AWS), Microsoft, and Google—have data centers full of powerful servers in locations around the world, and you share these resources with millions of other users, though each account is separate. Venders create software and applications that you pay to use or have available as free, open-source versions; you download them and start working away.
Some public cloud services, such as search engines and web-based email, are free, though you do have to endure advertising, and the companies providing these services are collecting your data for their own purposes—that’s how they can continue doing this without charging. You can pay for other public cloud services through subscriptions that give you unlimited access, or use on-demand or pay-per-usage pricing, where you pay only for what you need or what you use (similar to the way you pay for electricity). You can scale up to get extra services and extra data storage as necessary, then scale down when you no longer need them.
The three common types of cloud computing services can have overlapping applications: Infrastructure as a Service, or IaaS; Software as a Service, or SaaS; and Platform as a Service, or PaaS.
IaaS offers hardware such as servers, operating systems, and storage, such as a virtual data center, but you only have to pay for what you consume. With SaaS, you are using a remote software application that is managed by a third-party vendor and delivered via the internet, and you access it from a web browser rather than downloading it. PaaS delivers a framework that developers can build on and create custom applications; it includes servers, storage, and networking.
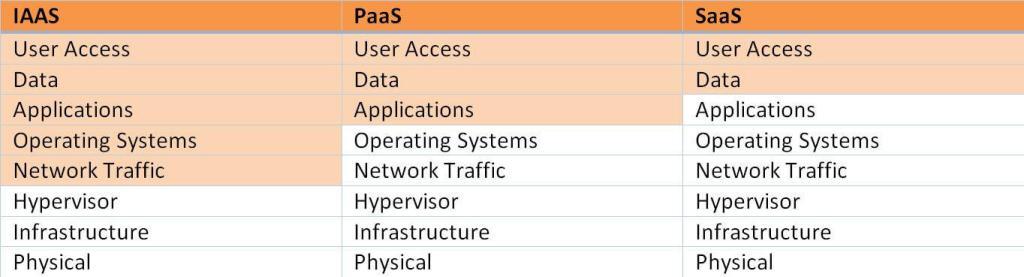
By providing effortless access to unlimited storage, all kinds of software and applications, and development platforms to create custom applications, Cloud computing offers your company almost endless possibilities to harness the internet’s vast resources. But though you can take much about the Cloud for granted, there is one crucial aspect you should not: Security. Do not assume the CP is keeping your data as safe and as protected as you want and need. You should stay on top of that and be sure you know what your responsibilities are and what the CP is supposed to do. In the table below, your responsibilities as the customer are shaded in orange, depending on the type of cloud computing service you are using.
At TalaTek, we researched all the options for building our SaaS, TiGRIS, and found that AWS offered the best security services for our needs. We do business with the federal government, so our SaaS must be FedRAMP accredited—that ensures we are offering government clients a secure Cloud system. AWS has developed security services specifically designed to address these security requirements. We can trust the AWS services we use in TiGRIS because they are FedRAMP approved, and AWS has the compliance documentation to prove it. This means the FedRAMP assessor validating our SaaS built with AWS services does not have to validate and review each separate service’s back-end security. This saves time and money.
And many AWS services/programs are also accredited by a myriad of security frameworks, such as ISO, FISMA, and HIPAA; if we want TiGRIS to be accredited by other security frameworks, we know we are compliant. Another reason we like AWS: it has clear, easy-to-access documentation, training resources, how-to guides, and other useful materials on its website that answer a lot of our questions—and save us time on hold or waiting for call backs from the help desk.
Of course, you may find that a different cloud provider meets your needs. There are several of them, and they all have pros and cons. But be sure that their security services are at the top of your list when researching their features, such as:
- Are they compliant with/accredited by common security frameworks such as FedRAMP, FISMA, ISO, and others?
- Do they highlight their security offerings on their website? What kind of technical support to they offer? Do they have useful materials on their website?
- Do they have a clear customer/CSP responsibility matrix that spells out inheritable controls?
- Is the CP just for federal government use, or is it commercially available?
So once you find the secure CP that meets your needs, dive in and get started. With the Cloud, the sky’s the limit.