Achieve CMMC 2.0 Compliance
CMMC 2.0 Compliance Is Now an Official Requirement for DIBThe Cybersecurity Maturity Model Certification (CMMC) 2.0 is official! CMMC assessment requirements will be rolled out in four phases over the next three years. The first phase was implemented November 10, 2025, with full implementation planned to be in place by November 10, 2028.
Organizations wanting to do business with the Department of Defense (DoD) must show they are CMMC compliant by going through a CMMC assessment by a certified third-party assessment organization (C3PAO).
TalaTek is a C3PAOs and can perform these assessments.
What Is CMMC?
CMMC is a DoD-mandated security framework for defense industrial base (DIB) organizations wanting DoD contracts. It is designed to enforce protection of Federal Contract Information (FCI) and Controlled Unclassified Information (CUI).
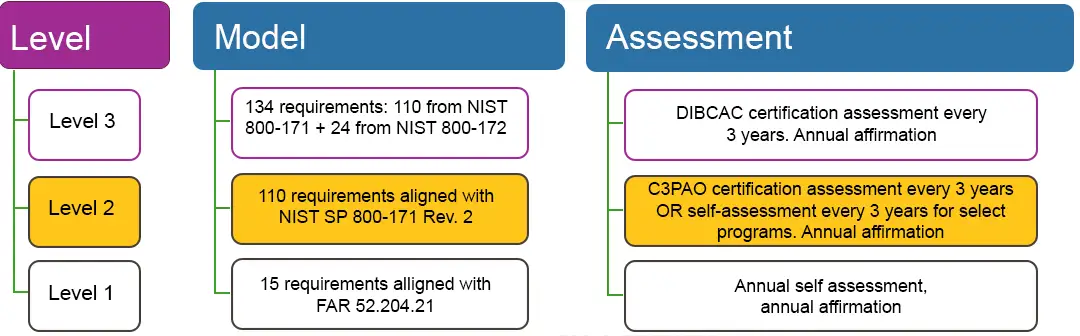
The gist of the program is that an organization can get certified at one of three levels—from Level 1, Basic Safeguarding of FCI, to Level 3, Higher-level Protection of CUI Against Advanced Persistent Threats. Each level has an increasing number of practices and processes that a DIB must implement to be in compliance with that level; those that are entrusted with FCI or CUI must achieve a specific Level as a condition of DoD contract awards.
Most DIB organizations that handle CUI will start with Level 2 certification (see the figure, below), which is based on 110 requirements aligned with NIST SP 800-171, Rev. 2, Protecting Controlled Unclassified Information in Nonfederal Systems and Organizations.
How Can My Organization Get Level 2 Certified?
As a C3PAO, TalaTek will assess the core components of your Level 2 environment: your defined CUI boundary, whether you follow the 110 NIST SP 800-171 Rev. 2, practices, and if you have complete documentation/evidence to show you do. Our assessment will follow the CMMC assessment process (CAP). Our final report will include scorings, detailed findings, and clear guidance on how you can remediate the findings. We will also prepare and submit the assessment package according to CAP requirements.
Why TalaTek?
TalaTek is a C3PAO, certified by the Cyber AB to ensure successful CMMC implementation, and we are listed on the Cyber AB marketplace: https://cyberab.org/Member/C3PAO-10036-Talatek.
We are also a FedRAMP 3PAO since 2014, are a cloud service provider with our own FedRAMP-accredited GRC solution, and have 16+ years of experience assessing both federal and commercial environments.
Our Comprehensive C3PAO audit comprises the following steps:
• Hold assessment kickoff/opening briefing
• Examine and analyze artifacts
• Conduct interviews and analyze results
• Observe tests and analyze results
• Verify objective evidence (OE) and record gaps
• Update OE review approach and status
• Rate practices and validate preliminary results
• Determine and record initial model practice ratings
• Generate preliminary recommended findings
• Validate preliminary recommended findings and ratings
• Generate final recommended assessment results
• Determine final practice pass/fail results
• Determine level recommendation
• Create and finalize recommended final findings
Additional CMMC Services
We also provide the following CMMC services that can help organizations seeking certification (OSC) prepare for their CMMC audit:
Basic Readiness
• Documentation development and gap analysis for compliance readiness
• Gap analysis: Review of current security posture against CMMC Level 2 or NIST 800-171 requirements
• Documentation development: Create or refine key documents such as the System Security Plan (SSP) and Plan of Action & Milestones (POA&M)
• Policy and procedures: Delivery of baseline templates tailored to the client’s environment
• Initial evidence collection guidance: Support in identifying and organizing objective evidence for future audits
• Readiness briefing: Summary of findings and next steps to prepare for full advisory or audit phases
Full Advisory
• Everything in Basic Readiness, including gap analysis, SSP/POA&M development, and policy templates
• 12 weeks of advisory support to guide remediation, implementation, and documentation alignment
• Control implementation guidance tailored to the client’s Azure and enclave environment
• Evidence preparation support to help collect, organize, and validate objective evidence for each control
• Weekly or biweekly check-ins to track progress, resolve blockers, and adjust the compliance roadmap
Audit Support Add On for Organizations Undergoing a CMMC Audit
• Support during the C3PAO audit phase, including evidence prep and assistance
• Pre-audit readiness review: Final check of documentation, objective evidence, and control implementation
• Evidence mapping assistance: Help aligning collected evidence to CMMC/NIST controls for auditor review
• Interview preparation: Coaching for key personnel expected to participate in the C3PAO audit
• Real-time audit support: On-call availability during the audit to clarify documentation, provide additional evidence, or respond to auditor questions
• Post-audit debrief: Review of preliminary findings and guidance on addressing any residual gaps or follow-up actions
Mock Audit
• Mock audit to simulate C3PAO assessment and identify final gaps
• Simulated C3PAO assessment: Conducted as if it were a real audit to test readiness under realistic conditions
• Objective evidence review: Evaluation of submitted documentation and artifacts to identify gaps or weaknesses
• Practice scoring and feedback: Preliminary scoring of practices with explanations for any deficiencies
• Interview simulation: Practice sessions with key personnel to prepare for actual auditor interviews
• Gap report & recommendations: Detailed findings report with prioritized remediation guidance
Gap Assessment Only
• One-time assessment to identify compliance gaps without remediation
• Initial discovery session: Understand the organization’s environment, scope, and compliance goals
• Control-by-control review: Evaluate current practices against CMMC Level 2 or NIST 800-171 requirements
• Evidence Check: Identify missing or insufficient documentation and technical controls
• Findings Report: Deliver a detailed gap analysis highlighting areas of non-compliance
• Remediation Roadmap (optional): High-level recommendations for closing identified gaps
GRC Continuous Monitoring over the 3-year period
• Leverages our FedRAMP-accredited GRC platform for assessment automation
• Streamlines evidence collection, control tracking, and reporting
• Supports CMMC compliance lifecycle with automated workflows
• Provides continuous monitoring and compliance health checks
• Maintains documentation and evidence for 3-year audit cycle
Contact Us Today
Schedule your Level-2 assessment or find out more about our CMMC services